This is an old revision of the document!
reCAPTCHA
As of LiteSpeed WebServer 5.4RC1, reCAPTCHA is available as a method of defense against DDoS attack.
How To Enable at the Server Level
Access the WebAdmin console via https://YOUR_SERVER_IP:7080
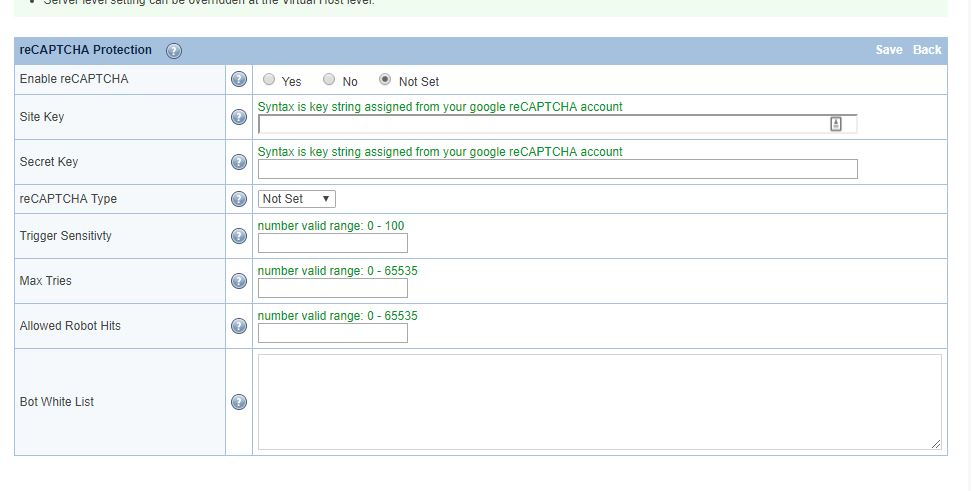
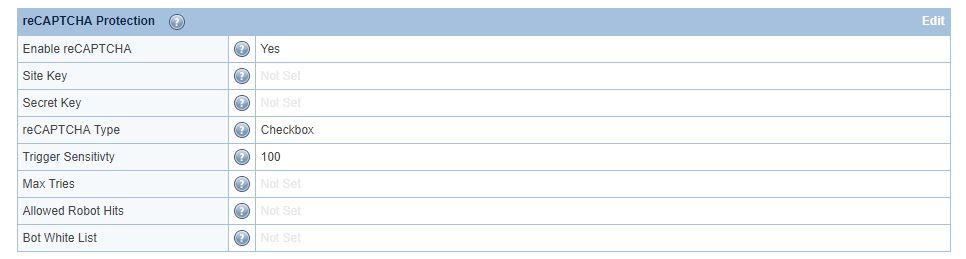
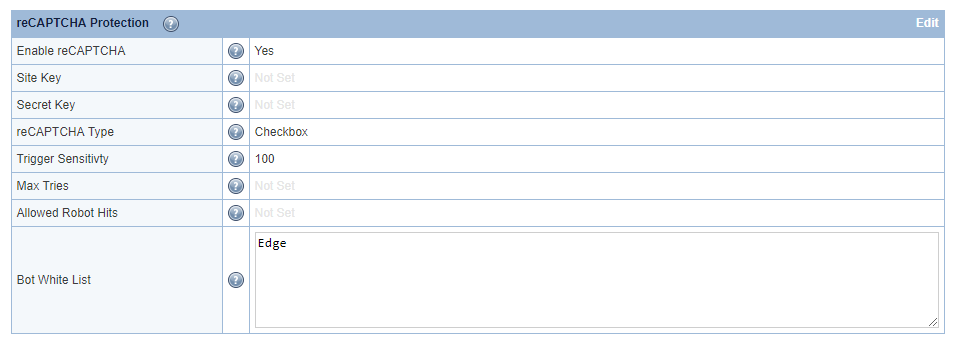
Navigate to Configuration → Server → Security → reCAPTCHA Protection
Set Enable reCAPTCHA to Yes. This is the master switch.
For other options, hover over the ? symbol to view detailed information about that option.
For demonstration purposes, we will set Trigger Sensitivity to maximum (100), and reCAPTCHA Type to Checkbox. You may adjust these values according to your needs. Save and restart LSWS.
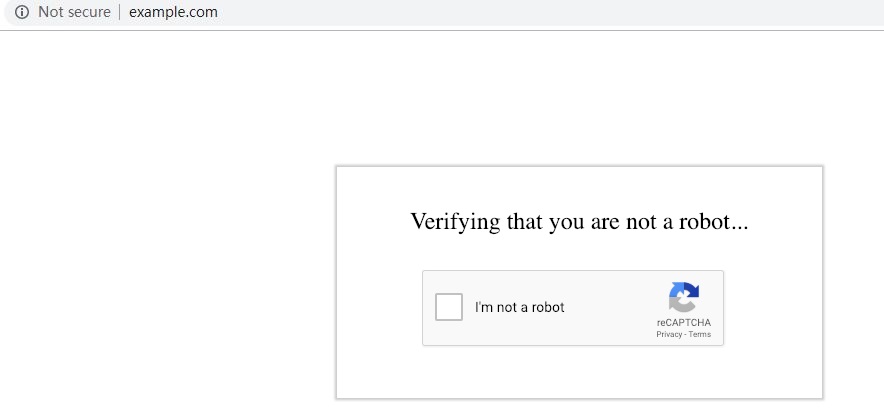
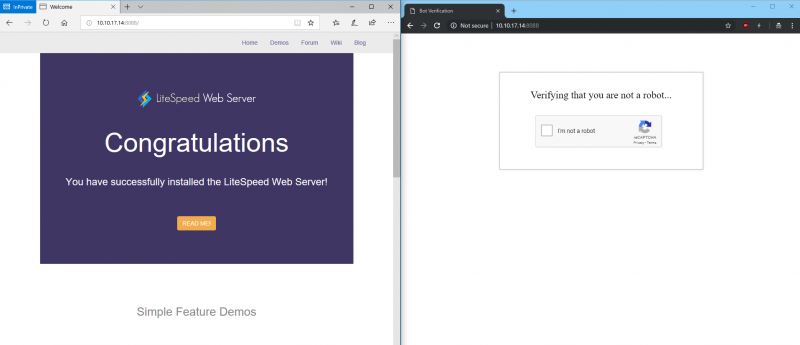
When a visitor accesses the website , they will need to go though reCAPTCHA validation to protect against a DDoS attack such as HTTP Flood.
You can also enable reCAPTCHA on an individual virtual host that is under attack, while leaving other websites disabled.
How To Enable at the Vhost Level
Server-level reCAPTCHA must be enabled.
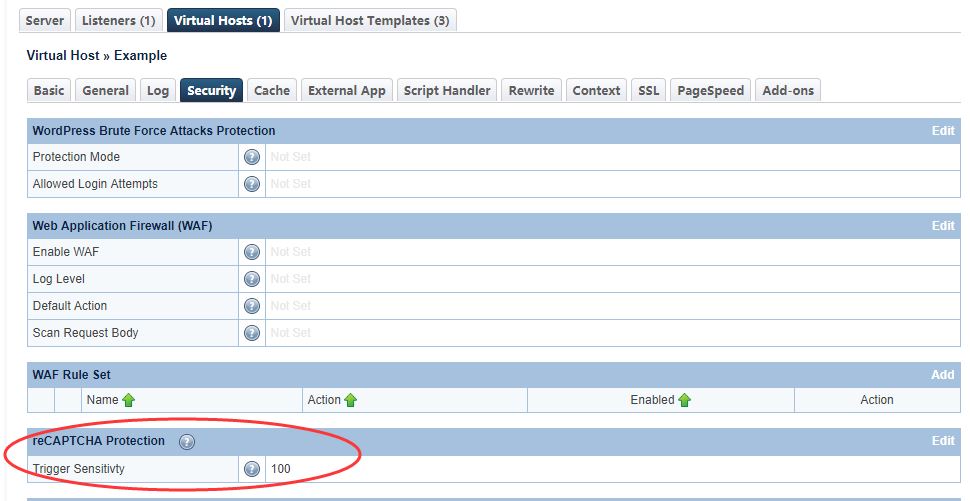
Please note that virtual-host-level sensitivity will override the sensitivity set at the server level.
You can enable virtual-host-level reCAPTCHA through rewrite rules or the WebAdmin console.
Rewrite Rule
Use one of the following rewrite rule directives:
[E=verifycaptcha] or [E=verifycaptcha: ACTION]
[E=verifycaptcha] will always redirect to reCAPTCHA until verified. ACTION can be deny to return a 403 or drop to drop the connection when Max Tries is reached. Until Max Tries is reached, the client will be redirected to recaptcha.
For example:
RewriteCond SOME-CONDITIONAL-CHECK RewriteRule .* - [E=verifycaptcha]
(SOME-CONDITIONAL-CHECK would be a suspicious UA, IP address, etc.)
LiteSpeed Native Mode
You can also use LSWS WebAdmin console to enable reCAPTCHA in LSWS native mode.
Navigate to Configuration → Virtual Hosts → Security → reCAPTCHA Protection
Customizing the Good Bots List
Google bots are considered good bots because they help index your site. However, they cannot do their job properly without receiving the correct page. The Bot Whitelist configuration may be used to specify bots that you may need for your site.
Here, we have configured 'Edge' in the Bot Whitelist text area. Bot Whitelist is a 'contains' match, but regex may be used as well.
After restarting, browsers containing Edge in the user-agent header will bypass recaptcha:
The Allowed Bot Hits configuration may be used to limit how many times a good bot (including Googlebot) is allowed to hit a URL before it is redirected to recaptcha as well. This may be useful to prevent bad actors from bypassing recaptcha using a custom user agent.
Customizing the Recaptcha Page
The default recaptcha page is generic. If you would like to customize the page, you may do so by creating a file at $SERVER_ROOT/lsrecaptcha/_recaptcha_custom.shtml.
There are two script tags that are required and it is strongly recommended to avoid changing the form and the recaptchadiv unless you know what you are doing. There are three echos within the page itself. Those are used by the web server to customize the recaptcha type and keys and specify any query string used.
Beyond those required attributes, everything else is customizable. As noted before, please ensure that you have backups of the default page and your customized page. Note that the .shtml extension is required in order to use the LSWS configured type and keys.