This is an old revision of the document!
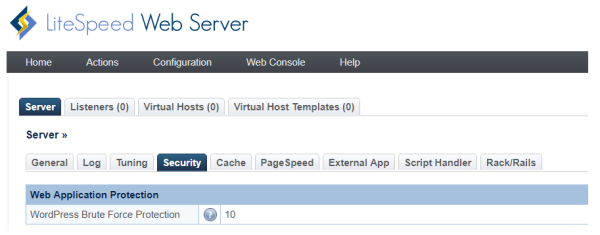
How to use web application protection
This function will protect wp-login.php and xmlrpc.php pages from brute force attack by POST method.
Requirement
LiteSpeed Web Server version 5.2.3+
How Brute Force Protection works
Specifies the maximum number, when wp-login.php and xmlrpc.php pages attempts allowed within 5 minutes before the IP is blocked.
This limit is handled using a quota system where limit = quota. Each POST attempt will decrease the quota by 1 with the quota increasing back to the set limit over time. The IP will be throttled starting at half of the limit, slowing more as the quota drops further. When the quota reached 0, the IP is blocked.
- For Example: If the limit is 10, it start to throttle when there are more than 5 attempts within the short period of time. It is a quota system, that each IP get quota of 10, each attempt will reduce it. and after 30 second, quota will increase 1. Once quota reach 0, the client will be blocked. So, it is not reset all at once, but gradually increase to the maximum if not keep hit the URL.
For cPanel Setup Method
The Syntax of Apache configuration directive: WordPressProtect (0|1|5-1000)
- 0 will disable it.
- 1 will enabled it. Use the server level config as default, if not set it is 10.
- Within 5-1000 will adjust the limit
Depends on which level you need to add the following lines to Server Level / Virtual Host Level / .htaccess
<IfModule Litespeed> WordPressProtect 10 </IfModule>
On Server level
- For EA3
/usr/local/apache/conf/includes/pre_main_global.conf - For EA4
/etc/apache2/conf.d/includes/pre_main_global.conf
On Virtual Host level
- For EA3
/usr/local/apache/conf/userdata/lscache_vhosts.conf - For EA4
/etc/apache2/conf.d/userdata/lscache_vhosts.conf
Design logic
- Virtual Host protect settings can rewrite both Server Level and .htaccess file
- .htaccess file can rewrite Server Level only
| Server Level | VHost Level | .htaccess | Result |
|---|---|---|---|
| 5 | x | x | 5 |
| 5 | x | 20 | 20 |
| 5 | 10 | x | 10 |
| 5 | 10 | 20 | 10 |