This is an old revision of the document!
How to enhance Plesk's security feature by enable TLS 1.3 and disable weak cipher suits.
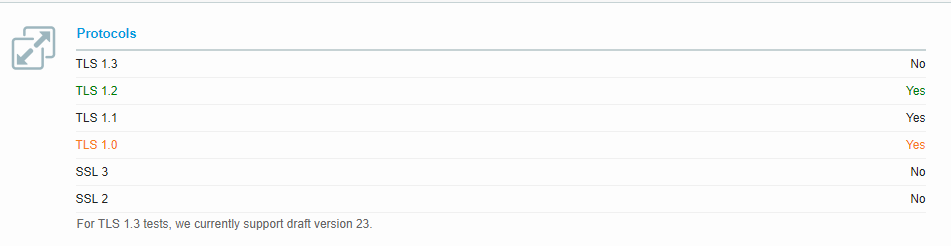
By default, Plesk configuration enables TLS1.0 , TLS1.1 and TLS1.2.
This guide will show you how to enable TLS 1.3.
This guide is made and tested on Plesk 17.8 and Centos 7.5.
For Debian/Ubuntu Plesk ,configuration files should be located in /etc/apache2/mods-available/ssl.conf.
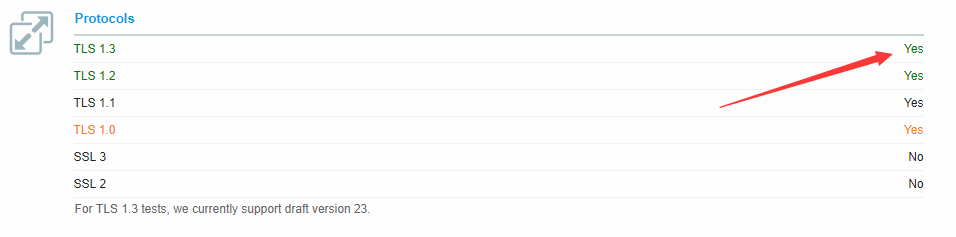
Enabling TLS1.3
Edit file /etc/httpd/conf.d/ssl.conf.
Find following line:
SSLProtocol +TLSv1 +TLSv1.1 +TLSv1.2
Replace it with following:
SSLProtocol TLSv1.1 TLSv1.2 TLSv1.3
This is enables TLS1.1 , TLS1.2 and TLS1.3
So in case if you want to disable TLS1.1 as well, then make it:
SSLProtocol TLSv1.2 TLSv1.3
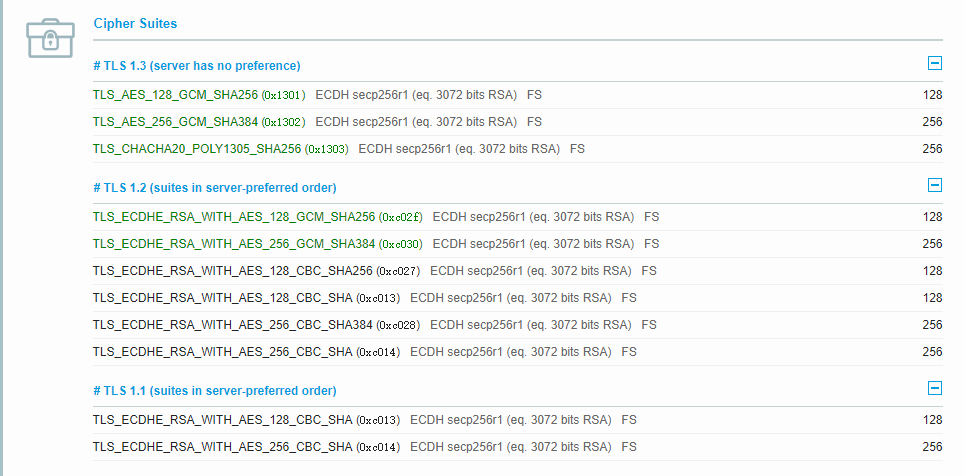
Disable Weak Cipher Suits (Optional)
By default, Plesk also comes with some weak cipher suites, if you also want to disable weak cipher suites, find the following lines:
SSLCipherSuite HIGH:!aNULL:!MD5
And replace it with:
SSLCipherSuite TLS_CHACHA20_POLY1305_SHA256:TLS_AES_128_GCM_SHA256:TLS_AES_256_GCM_SHA384:TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256:TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384:TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256:TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA:TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384:TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA:TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA:TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
Be aware, this may cause CPU load.
Test is done through SSL Lab